Risk Assessment and Control Evaluation
Commercial Internet Banking Risk Assessment and Controls Evaluation
Purpose
The following internet banking risk assessment and controls evaluation is provided to help commercial internet banking users identify threats and measure the strength of their controls.
Risk Assessment Questions
For each question, select the answer that best represents your environment. Following the assessment, use the “Control Evaluation – Best Answers and Tips” to evaluate your environment.
Personnel Security
1) Are employees required to sign an Acceptable Use Policy (AUP)?
a) Yes, at least annually or more frequently, as needed (1)
b) Yes, but only at hire (2)
c) No (5)
2) Does each employee using internet banking go through security awareness training?
a) Yes, at least annually or more frequently, as needed (1)
b) Yes, but only at hire (2)
c) No (5)
3) Do you complete background checks on employees prior to hire?
a) Yes, for all employees (1)
b) Yes, but only based on position (2)
c) No (5)
System Security
4) Is a dedicated system used for internet banking activities?
a) Yes, the system is dedicated to only internet banking activities (1)
b) No, the system is used for other business purposes (5)
5) Do systems have up-to-date antivirus software?
a) Yes, all systems (1)
b) Yes, but only critical systems (3)
c) No (5)
6) Is there a process in place to ensure software updates and patches are applied (e.g., Microsoft, web browser, Adobe products, etc.)?
a) Yes, a formal process where updates are applied on a regular basis(1)
b) Yes, but only as needed (3)
c) No (5)
7) Do users run as local administrators on their computer systems?
a) No (1)
b) Yes, but only those who require it (3)
c) Yes (5)
8) Does a firewall protect the network?
a) Yes (1)
b) No (15)
9) Do you have an Intrusion Detection/Prevention System (IDS/IPS) in place to monitor and protect the network?
a) Yes (1)
b) No (3)
10) Is internet content filtering being used?
a) Yes, internet traffic on the system used for “high risk” internet banking activities is restricted to approved sites, needed for business functions (1)
b) Yes, we have internet content filtering (2)
c) No (5)
11) Is email filtering being used?
a) Yes (1)
b) No (5)
12) Are users of the internet banking system trained to manually lock their workstations when they leave them?
a) Yes, and the systems are set to timeout after a period of inactivity (1)
b) Yes, but timeout is not enabled (2)
c) No (5)
13) Is wireless technology used on the network with the internet banking system?
a) No (1)
b) Yes, but wireless traffic uses industry-approved encryption (1)
c) Yes, but wireless uses weak encryption (2)
d) Yes, and wireless traffic is not encrypted (15)
Physical Security
14) Are critical systems (including systems used to access internet banking) located in a secure area?
a) Yes, behind a locked door (1)
b) Yes, in a restricted area (2)
c) No, in a public area (5)
15) How are passwords protected?
a) Passwords are securely stored (1)
b) Passwords are not securely stored (e.g., written on paper or sticky notes) (15)
Previous Experience
16) Have you experienced fraud through internet banking in the past?
a) No (1)
b) Yes, attempted fraud, but it was detected and stopped (3)
c) Yes (5)
17) Has malware been discovered on systems used for internet banking activities in the past?
a) No (1)
b) Yes (5)
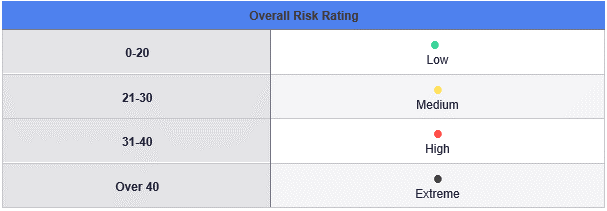
Risk Rating
Once you have completed the questionnaire, total the answers selected to calculate a summary risk rating of your environment. Note: This risk rating is designed to give a general idea of your risk posture based only on the answers in this questionnaire. Additional factors could either increase or decrease the risk.
Control Evaluation – Best Answers and Tips
Below are the results from the risk assessment. Review your answers and the tips to help you protect your systems and information.
- The best answer is “a) Yes, at least annually or more frequent as needed.” An Acceptable Use Policy (AUP) details the permitted user activities and consequences of noncompliance. Examples of elements included in an AUP are: Purpose and scope of network activity; devices that can be used to access the network, bans on attempting to break into accounts, crack passwords, circumvent controls or disrupt services; expected user behavior; and consequences of noncompliance.
- The best answer is “a) Yes, at least annually or more frequently as needed.” Security Awareness Training (SAT) for internet banking users should include, at a minimum, a review of the acceptable use policy, desktop security, log-on requirements, password administration guidelines, social engineering tactics, etc.
- The best answer is “a) Yes, for all employees.” Companies should have a process to verify job application information on all new employees. The sensitivity of a particular position or job function may warrant additional background and credit checks. After employment, companies should remain alert to changes in employees’ circumstances that could increase incentives for abuse or fraud.
- The best answer is “a) Yes, the system is dedicated to only internet banking activities.” It is best to have a dedicated system for high-risk internet banking activities.
- The best answer is “a) Yes, all systems.” Companies should maintain active and up-to-date antivirus protection provided by a reputable vendor. Schedule regular scans of your computer in addition to real-time scanning.
- The best answer is “a) Yes, a formal process where updates are applied at least monthly.” Update your software frequently to ensure you have the latest security patches. This includes a computer’s operating system and other installed software (e.g., web browsers, Adobe products, Microsoft Office, etc.). It is best to automate software updates when the software supports it.
- The best answer is “a) No.” Limit local administrator privilege on computer systems where possible.
- The best answer is “a) Yes.” Use firewalls on your local network to add another layer of protection for all devices that connect through the firewall (e.g., workstations, smart-phones, tablets, etc.).
- The best answer is “a) Yes.” Intrusion Detection/Prevention Systems (IDS/IPS) are used to monitor network/internet traffic and report or respond to potential attacks.
- The best answer is “a) Yes, internet traffic on the system used for “high risk” internet banking activities is restricted to only those sites specifically needed for business functions.” Filter web traffic to restrict potentially harmful or unwanted internet sites from being accessed by computer systems. For “high risk” systems, it is best to limit internet sites to only business sites that are required.
- The best answer is “a) Yes.” Implementing email filtering will help eliminate potentially harmful or unwanted emails from being delivered to end users’ inboxes.
- The best answer is “a) Yes, and the systems are set to timeout after a period of inactivity.” Systems should be locked (requiring a password to reconnect) when users walk away from their desks to prevent unauthorized access to the system.
- The best answers are either “a) No” or “b) Yes, but wireless traffic uses industry approved encryption.” Wireless networks are considered public networks because they use radio waves to communicate. Radio waves are not confined to specific areas and are easily intercepted by unauthorized individuals. Therefore, if wireless is used, security controls such as encryption, authentication, and segregation are necessary to ensure confidentiality and integrity.
- The best answer is “a) Yes, behind a locked door.” Physically secure critical systems to only allow access to approved employees.
- The best answer is “a) Passwords are securely stored.” Passwords should never be exposed to unauthorized individuals.
- The best answer is “a) No.”
- The best answer is “a) No.” If you have discovered malware on the internet banking system in the past, ensure the system is clean of all malware. It is best to do this by rebuilding the system.
Generated by Tandem Copyright © 2021